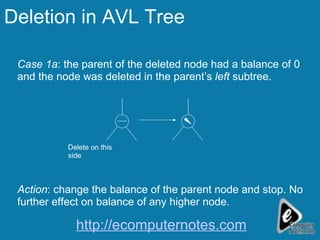
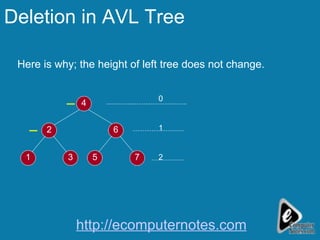
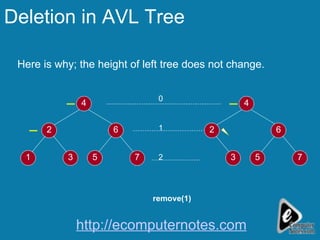
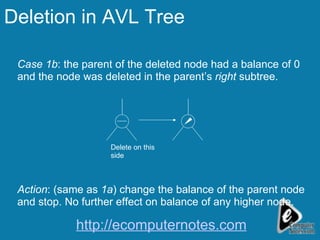
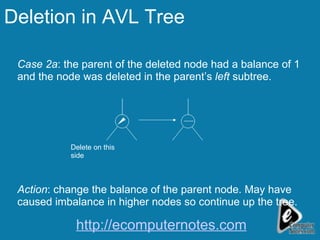
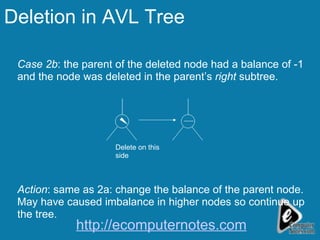
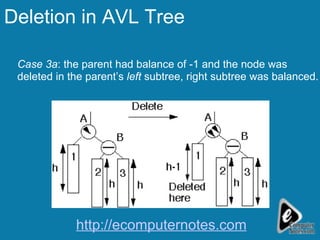
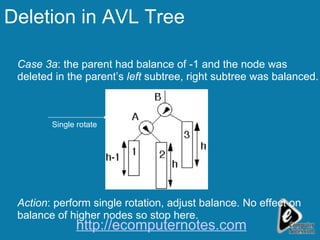
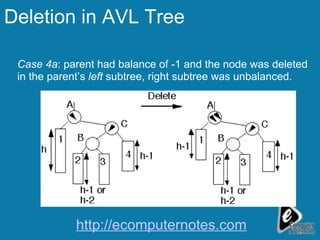
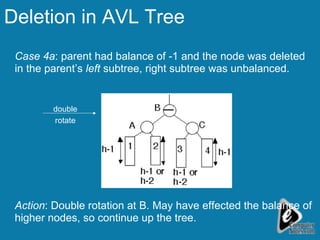
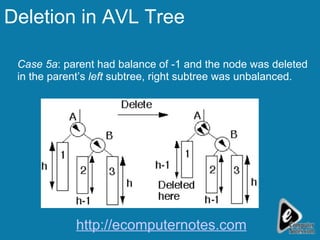
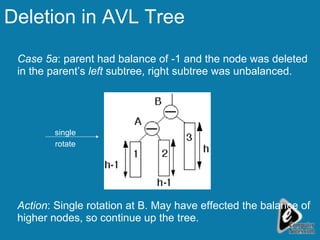
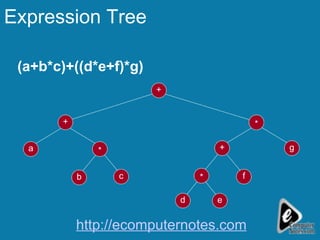
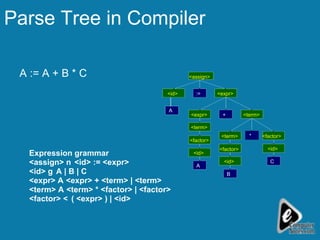
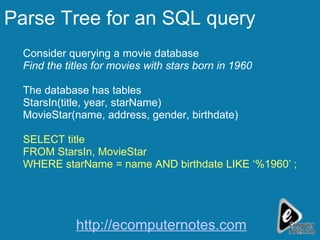
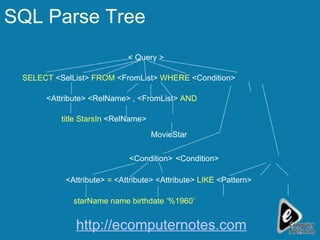
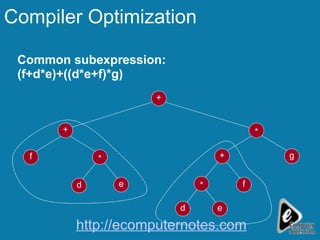
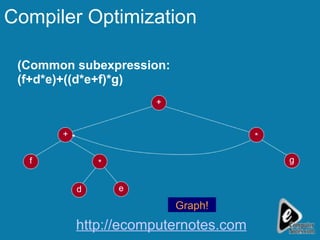
The document discusses deletion in AVL trees and outlines 5 cases to consider when deleting nodes from an AVL tree. It also discusses expression trees and parse trees, providing examples of an expression tree for a mathematical expression and a parse tree for an SQL query. Other uses of binary trees mentioned include their use in compilers for expression trees, parse trees, and abstract syntax trees.